
Cradlepoint Zscaler Internet Security
Policy in the Cloud, Enforcement at the Edge

Our Price: $240.00
Our Price: $720.00
Click here to jump to more pricing!
Overview:
Combined with Cradlepoint cloud-managed networking solutions, Zscaler Internet Security enables enterprises to embrace cloud applications and mobility, while delivering a superior user experience. Configured in minutes, Zscaler Internet Security leverages the threat intelligence harnessed from the Zscaler cloud. Now any business, regardless of size, can connect to the Internet with confidence.
- Increase network availability – provide protection from attacks, viruses and worms
- Simplify management – eliminate the need for standalone IPS devices at distributed locations
- Increase visibility – identify applications, devices, threats & vulnerabilities on network
- Protect data – prevent breaches while enabling regulatory PCI Compliance 3.0
URL Filtering
Limit exposure to liability by managing access to web content for enterprises across all distributed locations. URLs are filtered by global reputation—against more than 90 categories, 30 super categories, and 6 classes.
Low Latency and Transparent Redirection
Much more than domain filtering. Combine the simplicity of DNS and leverage the intelligence from proxy technology. Transparent redirection of traffic to enforce policies and protection guarantees a better end-user performance. Built-in fail open intelligence along with a reliable and redundant cloud guarantees zero downtime and no latency for enterprises.
Cloud Application Control
Leverage the power of cloud applications and social media without compromising productivity or security. Create global policies for webmail, streaming media, social and IM.
Unified Security Policy and Reporting
Create policies across security and Internet access management. Administrators manage their own policy—with changes instantly reflected across the cloud.
Benefits:
Secure Everywhere
Transparently enforce security & corporate policies from any device without impacting end-user experience.
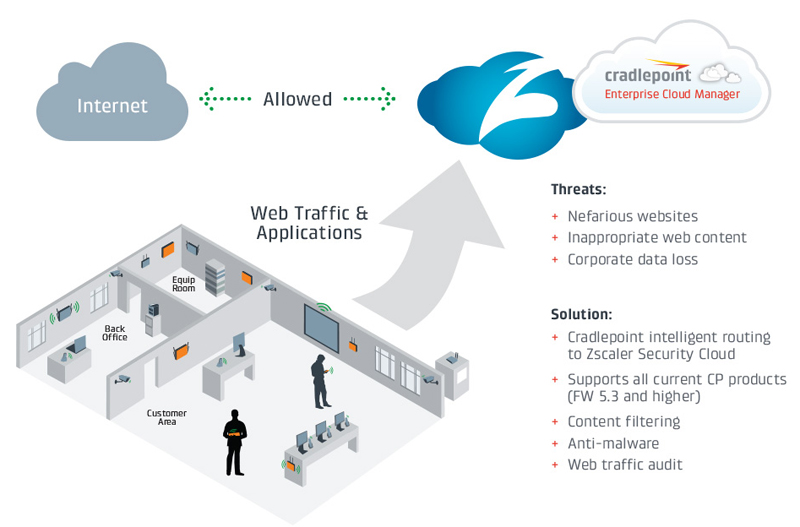
Direct-to-Cloud Security Powered by Zscaler
Consolidate Visibility
Intuitive dashboard provides instant insight into malicious activity and Internet browsing trends.
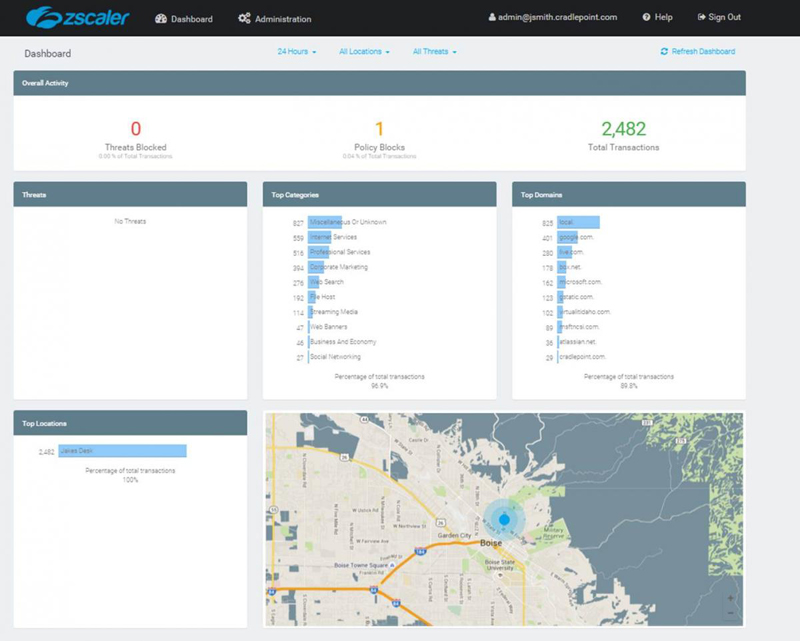
Zscaler Threat Dashboard
Ease of Deployment
Configure in minutes and filter domains for all Internet connection requests by intelligently routing traffic to permissible Internet sites and blocking access to known malicious / unauthorized sites.
Protect Your Business
Limit liability by filtering salacious sites and provide instant protection against malware, botnets, adware, phishing attacks, and suspicious destinations.
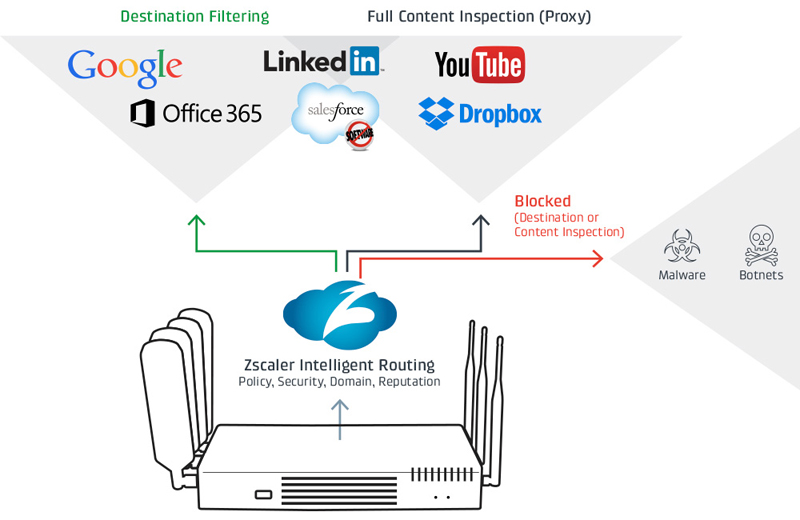
Intelligent Routing for Internet Bound Traffic
Manage Centrally
Select one of four risk tolerance settings to instantly enforce common policies. Alternatively, select specific Internet browsing categories to create a custom policy.
Scale Quickly
Cloud deployed and managed with no patching, no updates, and no buying excess capacity. Scale as you need capacity.
UTM Solution:
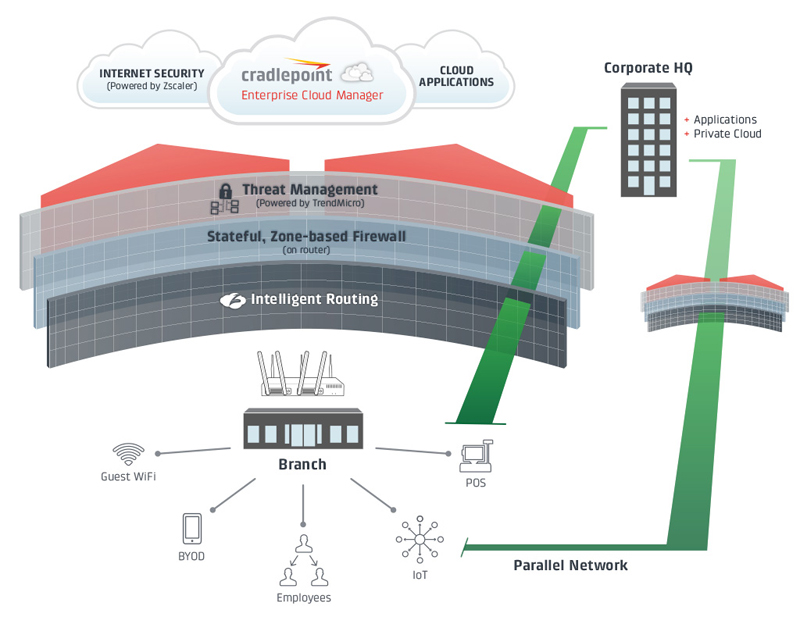
When purchased with CP Secure Threat Management, Zscaler Internet Security delivers a complete hybrid (On-Premise/Cloud-Managed) UTM Solution.
A Layered Security Approach for Defense In-Depth:
- Best-of-Breed Security Partners (Zscaler, Trend Micro, Asavie)
- Single management console
- Ideally sized for distributed enterprises
Specifications:
| Features | Zscaler |
|---|---|
| Coverage | |
| On-Network Devices | Any Device |
| Off-Network Devices - Windows & Mac | |
| Off-Network Devices - Android | |
| Global Datacenters for Traffic Processing | |
| Security | |
| Malware, Phishing, Botnet Protection | |
| Suspicious Destination Protection | |
| Adware Spyware | |
| Malicious Executables | Known Bad |
| Content Inspection | Suspicious Traffic |
| AV Inspection | Suspicious Traffic |
| Content Filtering | |
| 90+ Category Content Filtering | |
| White / Black Listing | |
Cloud Application Control
|
|
| Policies & Controls | |
| Real Time, Centralized Policy | |
| Global / Company Wide Policy | |
| Location-Based Policy | |
| Analytics & Reporting | |
| Real Time Dashboards & Log Drill Downs | |
| Analysis of “Other Traffic” Beyond Web | |
| Scheduled Email Reporting | Pre-defined Reports |
| Location-Based Reporting | |
| Support | |
| Web | |
| Telephone | Optional w/ TAM |
Supported Routers
- AER3100 Series
- AER2100 Series
- AER1600 Series
- COR IBR1100 Series
- COR IBR900 Series
- COR IBR600B Series
- COR IBR600C Series
- COR IBR600 Series
- ARC MBR1400
Frequently Asked Questions:
Product Licensing & Pricing
How is Zscaler Internet Security licensed?
Zscaler Internet Security is licensed on number of Cradlepoint devices forwarding DNS queries. Organizations should purchase one license per router forwarding the traffic to Zscaler.
How many users can I have at a location?
The service license per router allows for as many users as you need at the location, including GUEST WiFi filtering & security.
Should we contact Cradlepoint every time we add a new device?
Yes, every device requires a license. However, once you purchase the Zscaler Internet Security license, your admin can add/create the new location on the Zscaler portal without any involvement from Cradlepoint.
Should we contact Cradlepoint if we add more users to the location?
No, we do not price or license based on number of users from each location. However, we do monitor the number of DNS queries coming for each licensed device forwarding DNS queries to Zscaler Internet Security.
Device Configuration & Provisioning
How do I forward traffic to Zscaler Internet Security?
Cradlepoint recommends using router firmware 5.3 or higher with Zscaler Internet Security. With firmware 5.3 or higher, you simply edit the router’s configuration using Enterprise Cloud Manager or the local router UI: go to SECURITY > Content Filtering and select Cloud Based Filtering to set up Zscaler Internet Security.
How does my Cradlepoint router connect to the Zscaler Internet Security service?
Supported options for Cradlepoint routers with FW 5.3 and higher include:
- Fixed IP address: For locations with a fixed public IP address.
- DNS over TLS tunnel: For locations with dynamic IP addresses on the WAN side, (e.g. 4G cellular connections that are NAT’ed or ISPs that intercept DNS traffic to redirect to their DNS servers).
- DynDNS Service: For locations with dynamic IP address if the customer prefers to use DynDNS.
If they are public anycast DNS servers, anyone can use them. What is different?
Yes, they are public global DNS servers, and we do not restrict end users from using our DNS service and configuring Zscaler Internet Security servers for lookups. However, without registering with Zscaler as a customer, no security policies will be applied to the end user. It’s ONLY when the DNS queries are coming from a known customer, location and/or user, the company security policies will be applied. Otherwise, it is like any other DNS service the end user chooses to configure (similar to Google DNS).
How do you identify what company security policies to apply?
The customer’s Zscaler Administrator sets up a location through the Zscaler Portal, and then can assign content filtering and security policies to each individual location or groups of locations. Administrators can define as many policies as required, including custom policies, and manage these policies by location.
Can I create custom filtering and security policies?
Yes. Administrators can define any number of custom filtering and security policies. Administrators can select from 90+ categories for content filtering/classification. Administrators can also import custom URL categories and define as whitelist or blacklist policy. All security rules apply automatically to each Administrator-defined policy.
What if I have multiple WAN providers at the same location?
Administrators can add multiple (Public, TLS, or DynDNS) IP addresses per location in the Zscaler Portal. This will associate those providers IPs to the same location and will receive the same location policies during active/active or fail-over scenarios.
Security & Privacy Concerns
Is DNS-based filtering secure?
Zscaler Internet Security is configured by setting DNS to 8.34.34.34 and 8.35.35.35 – but it’s much more than traditional domain filtering. It combines the simplicity of DNS and the powerful functionality of proxy technology in an intelligent and transparent way. Network traffic is redirected using anycast technology to the nearest Zscaler Internet Security datacenter. Real-time threat intelligence and corporate policies are applied to route the traffic:
- Known malicious or unauthorized sites are blocked
- Access to reputable or permissible sites are allowed
- Potentially malicious or suspicious traffic that require deeper functionality and control such as Google safe search is routed through Zscaler’s proxy transparently. This dynamic inline inspection or traffic steering is called Intelligent Routing.
Can a user bypass Zscaler Internet Security security policy by going directly to the website’s IP address?
Possible, but extremely unlikely. Although Zscaler does not protect against direct IP-to-IP communication, most internet sites redirect IP connections back to DNS host names for various reasons, (e.g. most sites have many frames that load from several different services requiring DNS lookups, malicious sites don’t use fixed IP addresses, etc.).
Once the initial connection is attempted based on IP address, several additional DNS requests are made from the user’s browser, on behalf of the server, to various other destinations, which will then be enforced as normal through Zscaler Internet Security.
Can a user bypass the DNS settings on the router?
Cradlepoint router supports ‘force DNS’ to Zscaler DNS in the setup of Zscaler Internet Security (Enterprise Cloud Manager or locally). An administrator can have Enterprise Cloud Manager ‘lockdown’ the local router config so that no local users can change the configuration.
Does Cradlepoint or Zscaler have access to any private data within our organization?
No. Neither Cradlepoint nor Zscaler have access to any user data or information.
What information is stored within the Zscaler cloud?
DNS requests/responses, time stamps, and requesting locations’ identity for all requests sent to Zscaler Internet Security.
Zscaler Internet Security Performance
Will this security service add latency for end users?
No. For any user or device, on-premise or roaming, Zscaler Internet Security security service will add no noticeable latency (and it is possible that an end user’s performance will actually improve because Zscaler’s distributed service is peered with the top internet providers).
You are already using a cloud-delivered/ISP-offered external DNS service (such as Google or Level 3 DNS IPs), but your ISP does not offer any security policy or threat protection. With Zscaler Internet Security setup on your Cradlepoint router, it will use Zscaler DNS 8.34.34.34 and 8.35.35.35 to get the additional reliability and security
What happens when Zscaler Internet Security service is down?
Zscaler Internet Security service is a cloud-based offering, is always available, and is fully redundant and reliable. The Zscaler platform is physically running on thousands of processors in more than 100 of the highest quality data centers around the world. Each location has massive bandwidth, huge processing power and complete redundancy at every level. We provision our data centers so they have massive excess capacity – even during the largest global events like the World Cup or the Olympics we see a blip in traffic, but little more
In the rare case something fails, we have automatic failover within an individual data center, and then if an entire data center fails, we have additional automatic failover to the next nearest data center. This is totally seamless to your company and to your users. Zscaler is such a large and distributed and inherently resilient system it has literally never gone down – even during major disasters like hurricanes, earthquakes and typhoons that knock out individual data centers or even regions – the system as a whole always continues to run, and your users are automatically re-routed.
How scalable is the Zscaler solution?
Zscaler is a Security as a Service platform. With more than 5000 customers across all size enterprises and all vertical markets, Zscaler Cloud processes over 13 billion internet transactions every day – making it the single largest collection place for malware samples. This provides us a unique opportunity to analyze, identify and stop the most sophisticated and persistent threats.
The Zscaler platform is physically running on thousands of processors in more than 100 of the highest quality data centers around the world. Each location has massive bandwidth, huge processing power and complete redundancy at every level. We provision our data centers so they have massive excess capacity – even during the largest global events like the World Cup or the Olympics we see a blip in traffic but little more. All the service is built ground up by our engineering team and was built to handle scale. Add your locations instantly on our cloud platform, without any delay or impact to the existing solution.
Product Features and Functionality
Does Zscaler Internet Security replace my existing security point product solution?
Zscaler Internet Security provides several key components of a Unified Threat Management solution, and when used with Cradlepoint router/firewall platforms and CP Secure Threat Management, it delivers an effective layered security solution for the branch office.
The Cradlepoint router/firewall provides firewall protection for all WAN/LAN and LAN/ LAN segment traffic, and Zscaler Internet Security protects all the internet/web traffic.
Do I need Zscaler Internet Security when I have Cradlepoint Threat Management (IPS)?
Cradlepoint Threat Management (IPS) running on Cradlepoint’s stateful firewall, when combined with Zscaler Internet Security, addresses the key elements of a Unified Threat Management solution for branch offices.
Cradlepoint’s Threat Management solution provides additional layered security at the stateful firewall using Layer 4-7 Deep Packet Inspection to detect and prevent network intrusions. This enhances network security for all applications across LAN, WLAN and WAN segments. Zscaler Internet Security provides content filtering and security for all web-based applications and traffic.
Does Zscaler Internet Security provide antivirus protection?
Yes for known viruses. Zscaler Internet Security receives the same URL and threat feeds as the cloud proxy platform. The Zscaler Cloud Platform processes over 13 billion internet transactions every day – making it the single largest collection place for malware samples. This provides us a unique opportunity to analyze, identify and stop the most sophisticated and persistent threats. If we identify a virus on a network once, we can then block it via Intelligent Internet Protection.
However, any first time virus (to Zscaler cloud) or file cannot be blocked using Zscaler Internet Security as it is not an in-line proxy solution. Zscaler does not look at all the content.
In order to get always in-line content protection, upgrade to Zscaler Secure Web Gateway product. Cradlepoint routers also support Zscaler Secure Web Gateway (additional cost as licensed on a per-user basis).
Does Zscaler Internet Security block malicious attachments for webbased email?
Zscaler Internet Security does not scan attachments downloaded using mail applications. However, any malicious attachments that subsequently call web services (botnets, Command-Control Networks, etc.) will be blocked by Zscaler Internet Security for all known malware.
Does Zscaler Internet Security provide DLP solution?
No. Zscaler Internet Security does not look at the content. In order to get full content and data loss prevention, upgrade to Zscaler Secure Web Gateway product.
Does Zscaler Internet Security provide antispam solution?
No. Zscaler is not an email security platform. It will block and protect against any known malicious virus in the email attachment, and also block and protect against any malicious links clicked from within the email. However, it is not in-line between your exchange server and client to protect against spam.
Does Zscaler Internet Security inspect SSL traffic?
Yes. However, SSL inspection requires a certificate be installed on the end-user device in order for the SSL inspection to work.
What protections does Zscaler Internet Security provide for SSL traffic?
Zscaler’s SSL inspection provides protection across the same threat categories as non-encrypted traffic – filtered content sites, safe search results, malicious content, phishing, CnC botnets, etc., are all filtered and blocked.
When should SSL inspection be used?
Most often, the SSL inspection would be deployed on computers used by employees in the branch office where additional security is desired. SSL inspection is not advised for guest WiFi subnets.
How does Zscaler Internet Security compare to a URLlist filtering solution running on a firewall/ router?
Zscaler’s URL filtering capabilities are superior to legacy firewall and router-based solutions for the following reasons:
- Zscaler is ‘cloud real-time’ security and filtering with global threat intelligence updates immediately. No need for signatures/patches to be developed, downloaded, and deployed to the router/firewall. Zscaler currently averages over 100k threat updates per day, all in real-time. As soon as a new threat is discovered, the next transaction anywhere in our cloud is protected.
- Simple URL-based filtering on routers generally use a very static ‘reputation only’ list that is often out of date and incomplete. Zscaler’s real-time dynamic security cloud on the other hand uses a proprietary ‘Page Risk Index’ that utilizes many types of threat intelligence feeds and analytics to ensure that its list of compromised domains is the most accurate and effective on the market.
- Many of today’s hackers use exotic ‘fast flux’ techniques (rapid DNS name changes) to keep their web resources free from simple IP/URL based security branch router-based URL filtering can’t keep up to date with these threats as even high quality ‘reputation only’ block lists are often very slow to add these new domains.
- Zscaler cloud uses best-of-breed intelligence and reputational scoring based on billions of global web transactions every month, which delivers the most accurate, comprehensive and up-to-date web security and content filtering.
- The Zscaler cloud has virtually unlimited capacity - no processor or bandwidth limits to create a bottleneck or single point of failure. Customers have no risk of outgrowing equipment, as the cloud capacity scales with them.
Documentation:
Download the Cradlepoint Zscaler Internet Security Datasheet (.PDF)
Pricing Note:
- Pricing and product availability subject to change without notice.
- Enterprise Cloud Manager is required for centralized management and to enable networking applications.
Our Price: $240.00
Our Price: $720.00
